
The Next Vulnerability: Looking Back on Meltdown and Spectre One Year Later
Around this time last year, two vulnerabilities known as Meltdown and Spectre became public. Discovered

Around this time last year, two vulnerabilities known as Meltdown and Spectre became public. Discovered

Michael Cobb, certified information systems security professional – information systems security architecture professional (CISSP –

Anti-counterfeiting or ACF technology is becoming in greater demand in all industry sectors. It’s coming
EE Times India reports that the RISC-V instruction set architecture (ISA) has made significant progress in

Some of the top Rambus technical experts will hold forth at DesignCon 2019 in a
The latest news coming out of the security world is the link up of Micron’s

We will be showcasing our CryptoManager Root of Trust at the RISC-V Summit on December 3-6,2018, at

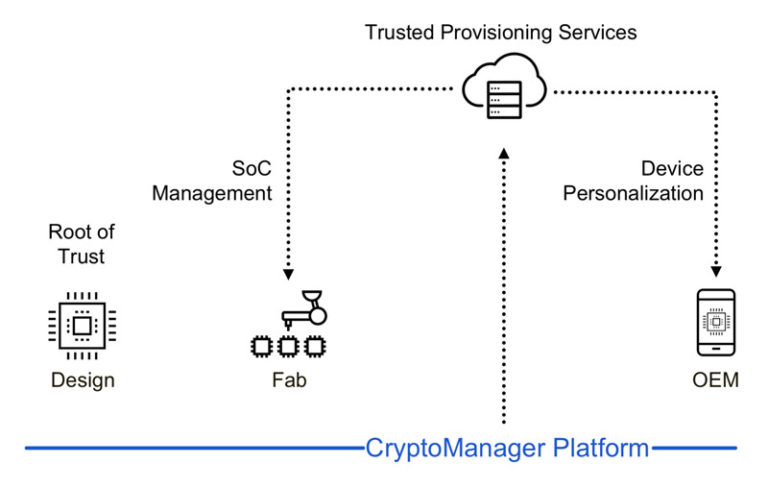
With the proliferation of connected devices and the sensitive data they produce comes a significant
On November 27th, Senior Vice President of Global Marketing, Sales and Support, Mike Noonen, will

The financial technology sector converged on Las Vegas for Money 20/20 last week, bringing together

Firefighters are battling three major California wildfires. One is in Northern California in Butte County;
Today, on October 16th, 2018, Rambus has announced the collaboration with Riscure, a global security

Our world is growing increasingly connected, and while most people have reaped the benefits of

People are living in an age with an unprecedented level of access to all kinds of information. Users of social media and networks can contact their far away friends in real time, and have access to events right as they develop. Such technology was the stuff of dreams, only imagined in science fiction stories in the late 20th century. Yet, the unprecedented access to citizens’ private information is something only imagined in George Orwell’s 1984 as well.
The single software ecosystem built on the RISC-V standard allows for OEMs to bypass having to lock into a specific processer ecosystem. When an OEM chooses a particular processor type, it not only has to pay for that particular processor, but it has to continue to purchase from whichever company it purchased it processor from, leading to a market where profits are not driven by competition

Dubbed “Foreshadow,” this speculative execution attack allows an attacker to steal sensitive information stored inside personal computers or third-party clouds. There are two versions: the original attack designed to extract data from Software Guard Extensions (SGX) enclaves and a next-generation version that affects virtual machines (VM), hypervisors, operating system kernel memory, and System Management Mode (SMM) memory. SGX is a new feature in modern CPUs which allows computers to protect users’ data, even if the entire system falls under the attacker’s control.

At the second annual DEF CON Voting Village, a part of the convention that seeks to exploit voting machines to better understand vulnerabilities, an 11-year old boy managed to hack into a replica of the Florida state election website, making it appear that 2016 independent presidential candidate Darrell Castle won the state.

In the age of cryptocurrency mining and with demand for memory getting higher, it is getting harder to find more affordable memory. Yet, there is a belief that RAM and graphics cards prices may be cheaper by about 25% in 2019.
Reduced Instruction Set Computing Five (RISC-V) is an open Instruction Set Architecture (ISA) designed with small, fast, and low-power real-world implementations in mind. It describes the way in which software talks to an underlying processor

According to a new report published by Bain and Company, the combined markets of the
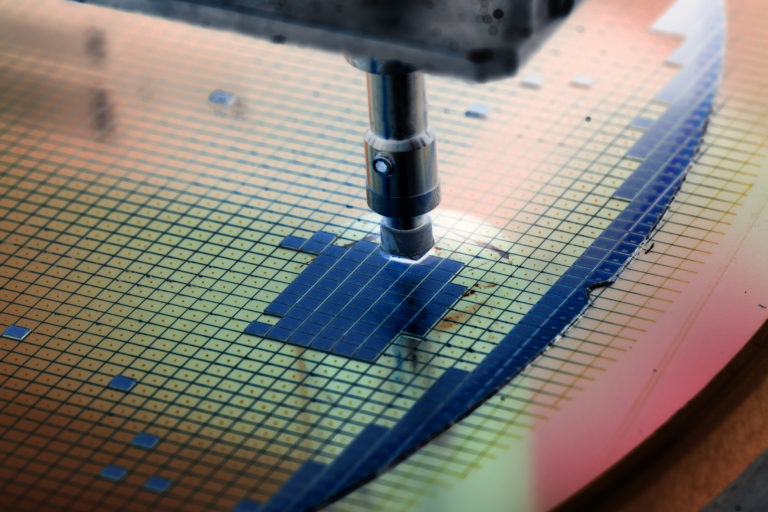
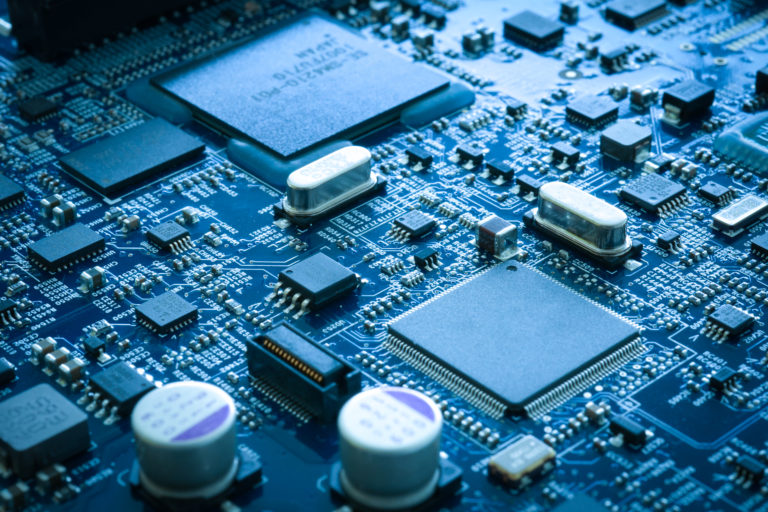
Last updated on: December 11, 2019 What’s the future of semiconductor industry? In an age
Subscribe to receive a weekly update from the Rambus Blog.
