ChaCha20 family of accelerators.
Supporting TLS1.3 IoT HomeKit.
Home > Security IP > Crypto Accelerator Cores > ChaCha-IP-13
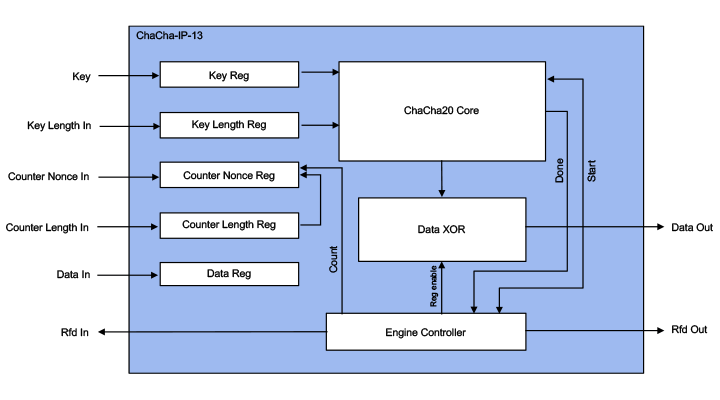
The ChaCha-IP-13 (EIP-13) is an IP solution for accelerating the ChaCha20 cipher algorithm (RFC7539), supporting the NIST CTR mode up to 12.8 Gbps @ 300MHz. Designed for fast integration, low gate count and full transforms, the ChaCha-IP-13 accelerator provides a reliable and cost-effective embedded IP solution that is easy to integrate into high-speed crypto pipelines.
ChaCha20 family of accelerators.
Available in three configurations / performance grades.
Supporting TLS1.3 IoT HomeKit.
The ChaCha-IP-13 is a family of the cryptographic library elements in the Rambus hardware IP library (formerly of Inside Secure). For example, the ChaCha-IP-13 is the cipher core embedded in the VaultIP root of trust security cores providing support for TLS1.3 and HomeKit IoT applications (ChaCha20 is also available as SW implementation in VaultIP cores). The accelerators include I/O registers, encryption and decryption cores, and the logic for feedback modes and key scheduling.
Sustained performance for any object sizes ranges from 2 to 12.8 Gbps depending on the configuration and area. Gate count is around 30K gates depending on the configuration.
Rambus also offers the required Poly1305 algorithm to match the ChaCha20 cipher in HomeKit.
Key benefits:
Features:
