Home > Security IP > Anti-Counterfeiting
CryptoFirewall Verifier and Consumable IP
The Rambus CryptoFirewall Verifier and Consumable IP cores are hardware-based security blocks designed to provide secure authentication and reduce counterfeiting business risk for mass-market consumables and peripherals. For consumable devices like printers, medical devices, batteries and automotive components where extending ‘time to clone’ is essential to business success, CryptoFirewall cores deliver robust anti-counterfeiting for revenue, safety, and brand protection.
Anti-Tampering Technologies

The design of chip anti-tamper protection needs to adapt and scale with rising threats. Adversaries range from high school hackers to well-funded state actors. Given the threats, it’s useful to think about anti-tamper countermeasures as a hierarchy of safeguards that parallel the type, effort and expense of attacks. Watch this webinar to learn the eleven kinds of tampering attacks and their required skills and resources, and countermeasures for each of these attacks.
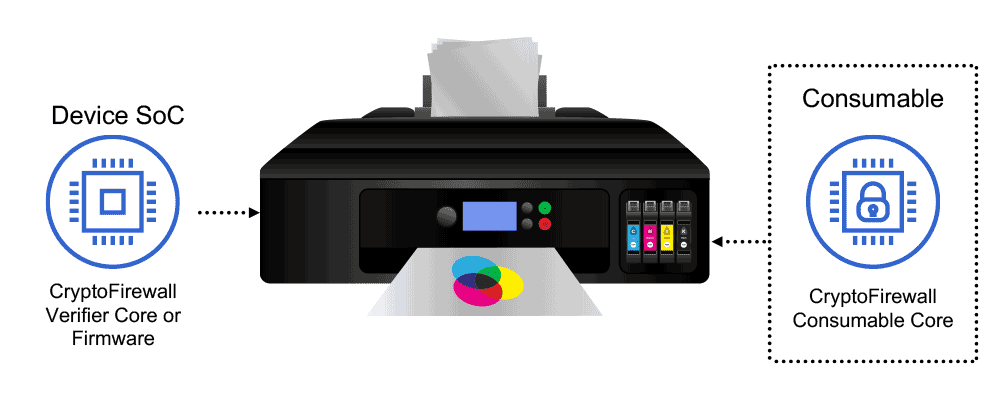
How the CryptoFirewall System Works
The Verifier core is a robust, anti-counterfeiting hardware core designed to provide authentication with the highest level of tamper resistance.
The core can be used in conjunction with the CryptoFirewall Consumable core as part of a complete consumable protection system. It integrates into the device SoC and communicates to the CryptoFirewall Consumable core to authenticate and verify system integrity of the consumable or peripheral.
The Verifier core monitors the balances of the usage counters within the Consumable core, denying authentication once the balance reaches zero.
The Importance of Chiplet Security
Chiplets are gaining significant traction as they deliver numerous benefits beyond what can be accomplished with a monolithic SoC in a time of slowing transistor scaling. However, disaggregating SoCs into multiple chiplets increases the attack surface which adversaries can exploit to penetrate safeguards to data and hardware. With chiplets, the risks of hardware-based trojans and exploits such as man-in-the-middle attacks all rise. To realize the many benefits of chiplets, designers should use a design for security approach, and implement security safeguards anchored in hardware.