Industrial IoT: Threats and Countermeasures
Industrial Internet of Things (IIoT) systems are improving service delivery and increasing productivity across a broad range of industries from manufacturing to health care. But as with anything connected to the internet, IIoT devices are subject to cyber threats. These include attacks on industrial control systems (ICS) such as distributed control systems (DCS), programmable logic controllers (PLC), supervisory control and data acquisition (SCADA) systems, and human machine interfaces (HMI). The adoption of increasingly powerful and complex IP-based devices, including the use of sophisticated microprocessors, comes with growing risk. Specific cyber-attacks aimed at IIoT infrastructure could include:
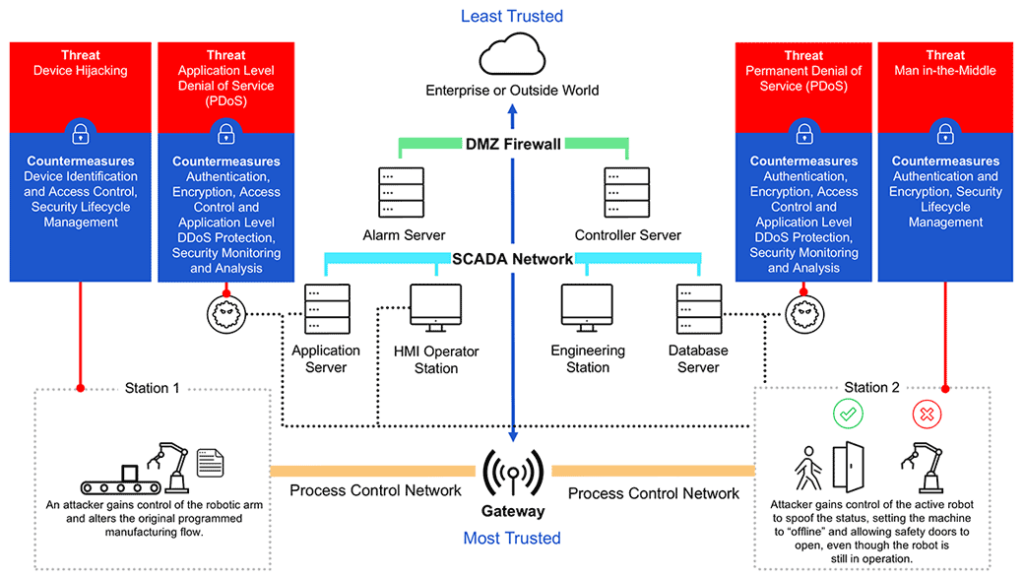
Man-in-the-middle: An attacker breaches, interrupts or spoofs communications between two systems. In an IIoT scenario, an attacker could assume control of a smart actuator and knock an industrial robot out of its designated lane and speed limit – potentially damaging an assembly line or injuring operators.
Device hijacking: The attacker hijacks and effectively assumes control of a device. These attacks are quite difficult to detect because the attacker does not change the basic functionality of the device. Moreover, it only takes one device to potentially re-infect others, for example, smart meters connected to a grid. In an IIoT scenario, a hijacker could assume control of a smart meter and use the compromised device to launch ransomware attacks against Energy Management Systems (EMSs) or illegally siphon unmetered power lines.
Distributed Denial of Service (DDoS): A denial-of-service attack (DoS attack) attempts to render a machine or network resource unavailable to its intended users by temporarily or indefinitely disrupting services of a host connected to the Internet. In the case of a distributed denial-of-service attack (DDoS), incoming traffic flooding a target originates from multiple sources, making it difficult to stop the cyber offensive by simply blocking a single source. DoS and DDoS attacks can negatively affect a wide range IIoT applications, causing serious disruptions for utility services and manufacturing facilities.
Permanent Denial of Service (PDoS): Permanent denial-of-service attacks (PDoS), also known as phlashing, is an attack that damages the device so badly that it requires replacement or reinstallation of hardware. BrickerBot, coded to exploit hard-coded passwords in IoT devices and cause permanent denial of service, is one such example of malware that could be used to disable critical equipment on a factory floor, in a wastewater treatment plant, or in an electrical substation.
Securing the Industrial IoT
IIoT infrastructure should be protected by a comprehensive set of security solutions that do not disrupt operations, service reliability or profitability. A practical and simple, yet secure solution that can be easily and widely adopted by IIoT device makers and their customers is more effective than a ‘super solution’ that fails to gain serious traction. Security solutions should include the following capabilities:

Firmware integrity and secure boot
Secure boot utilizes cryptographic code signing techniques, ensuring that a device only executes code generated by the device OEM or another trusted party. Use of secure boot technology prevents hackers from replacing firmware with malicious instruction sets, thereby preventing attacks. Unfortunately, not all IIoT chipsets are equipped with secure boot capabilities. In such a scenario, it is important to ensure that IIoT devices can only communicate with authorized services to avoid the risk of replacing firmware with malicious instruction sets.
Mutual authentication
Every time a smart actuator in the manufacturing floor connects to the network it should be authenticated prior to receiving or transmitting data. This ensures that the data originates from a legitimate device and not a fraudulent source. Secure, mutual authentication—where two entities (device and service) must prove their identity to each other—helps protect against malicious attacks. Cryptographic algorithms involving symmetric keys or asymmetric keys can be utilized for two-way authentication. For example, the Secure Hash Algorithm (SHA-x) along with hash-based message authenticated code (HMAC) can be used for symmetric keys and Elliptic Curve Digital Signature Algorithm (ECDSA) for asymmetric keys.

Secure communication (end-to-end encryption)
Secure communication capabilities protect data in transit between a device and its service infrastructure (the cloud). Encryption ensures that only those with a secret decryption key can access transmitted data. For example, a smart actuator that sends usage data to the SCADA must be able to protect information from digital eavesdropping.
Security monitoring and analysis
Security monitoring captures data on the overall state of an industrial system, including endpoint devices and connectivity traffic. Data is then analyzed to detect possible security violations or potential system threats. Once detected, a broad range of actions formulated in the context of an overall system security policy should be executed, such as revoking device credentials or quarantining an IoT device based on anomalous behavior. This automatic monitor-analyze-act cycle may execute in real time or at a later date to identify usage patterns and detect potential attack scenarios. It is critical to ensure that endpoints devices are secured from possible tampering and data manipulation, which could result in the incorrect reporting of events.

Security lifecycle management
The lifecycle management feature allows service providers and OEMs to control the security aspects of IoT devices when in operation. Rapid over the air (OTA) device key(s) replacement during cyber disaster recovery ensures minimal service disruption. In addition, secure device decommissioning ensures that scrapped devices will not be repurposed and exploited to connect to a service without authorization.
Rambus Security Solutions for Industrial IoT
Rambus offers a comprehensive suite of security solutions for safeguarding the chips and devices critical to IIoT. These include:
Root of Trust solutions provide the hardware-level foundation for security enabling functions such as secure boot, secure execution of applications, tamper detection and protection, and secure storage and handling of keys.
Protocol Engines secure network communications between IIOT devices and the cloud without altering the traffic. They enable secure end-to-end communications while maintaining vital network performance.
Provisioning and Key Management secure supply chain solutions for chip and IIoT device manufacturers enable secure key insertion and cloud-based device key management services.
