HASH-IP-57 hash accelerators, MD5, SHA-1, SHA-2, SHA-3 accelerators
Home > Security IP > Crypto Accelerator Cores > HASH-IP-57
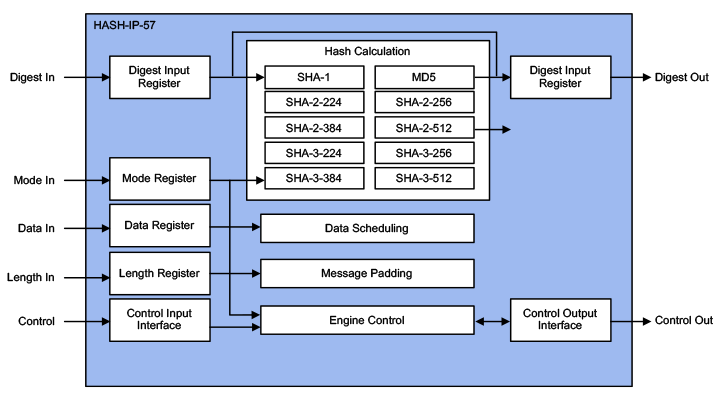
The HASH-IP-57 (EIP-57) is IP for accelerating the various secure hash integrity algorithms like MD5 (RFC1231), SHA-1 (FIPS-180-2), SHA-2 (FIPS-180-3/4) and SHA-3 (FIPS-202), supporting the NIST MAC mode up to 6.4 Gbps @ 450MHz. Designed for fast integration, low gate count and full transforms, the HASH-IP-57 accelerators provides a reliable and cost-effective embedded IP solution that is easy to integrate into high-speed crypto pipelines.
Secure Hash family of accelerators.
Available in several configurations / performance grades.
Library element for platform security and packet engines
How the HASH-IP-57 works
The HASH-IP-57 is a family of the cryptographic library elements in the Rambus hardware IP library (formerly of Inside Secure). For example, the HASH-IP-57 is the hash core embedded in the IPsec packet engines as well as VaultIP hardware root of trust cores providing support for MD5 and SHA Hash-based functions. The accelerators include I/O registers, encryption and decryption cores, and the logic for feedback modes and key scheduling.
Sustained performance for any object sizes ranges from 2 to 84 Gbps depending on the configuration and area. Gate counts ranges from 14K to 49K gates depending on the configuration.
HASH-IP-57 Information
Key benefits:
- Silicon-proven implementation
- Fast and easy to integrate into SoCs
- Flexible layered design
- Complete range of configurations
- World-class technical support
Features:
- Wide bus interface (1024-bit data, 512-bit digest) or 32 bit register interface
- MD5, SHA-1, SHA-2, SHA-3
- SHA-2/3 in 224/256/384/512 modes
- Message puffing for all algorithms
- Message data scheduling hardware
- Hash context switching and state loading
- Standard, high frequency and high performance versions available
- Fully synchronous design
Alternative:
- HMAC-IP-59 MD5, SHA-1, SHA-2, SHA-3 Hash based HMAC, accelerators