Home > Security IP > Root of Trust Solutions > RT-1660
The Rambus Root of Trust RT-1660 is a fully programmable, FIPS 140-3 compliant root-of-security core offering security by design for U.S. Defense mission-critical applications. The RT-1660 protects against a wide range of hardware and software attacks with state-of-the-art anti-tamper security techniques. U.S. Defense hardware requires the highest security protections due to sensitive information being stored and processed. The RT-1660 is a military grade security co-processor, built on a custom-designed 32-bit RISC-V architecture, along with dedicated, cryptographically secure memories.
The RT-1660 offers superior tamper resistance through the implementation of Differential Power Analysis (DPA) countermeasures and state-of-the-art fault injection attack (FIA) protections. The RT-1660 implements DPA and FIA protected AES, RSA, and ECC cryptographic accelerator cores. The RT-1660 provides HW implementations of a NIST SP800-90a/b/c compliant TRNG (true random number generator), Public Key Engine (RSA up to 8192 bits and ECC up to 521 bits), AES (all modes), HMAC and SHA-2/-3 crypto accelerators. The RT-1660 core is FIPS 140-3 CAVP/CMVP compliant. It is the ideal choice for chip and system architects designing FPGA and ASIC solutions for applications requiring the highest level of security.
Security in the ARM Ecosystem
Building security in an SoC aiming to meet the goals set by the ARM Platform Security Architecture (PSA) is a complex matter. This is compounded by the complexity of modern-day SoCs comprising multiple processors, security domains and security levels. The Rambus root of trust provides a solid foundation for the SoC security architecture ticking ‘all the boxes’ for reaching the security goals, while offering extensive support for effective integration into a complex TrustZone-based SoC infrastructure.How the Root of Trust Works
While built upon a RISC-V architecture, the 32-bit CPU in the RT-1660 is a custom implementation designed specifically for security use cases. Rambus employed over 20 years of device security experience to build a security co-processor providing the highest levels of siloed and layered security. The RT-1660 is designed for integration into military and government ASICs and FPGAs, offering secure execution of authenticated user applications, tamper detection and protection, and secure storage and handling of keys and security assets.
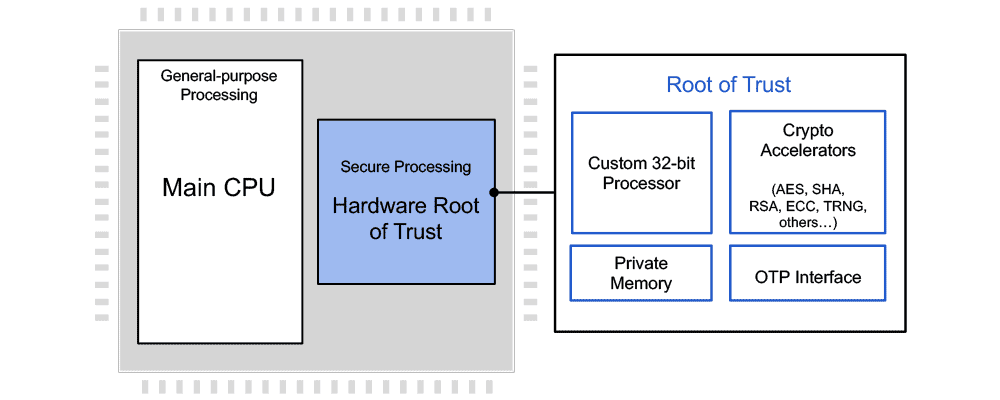
The Root of Trust offers a siloed approach to security. While located on the same silicon as the main processor, the secure processing core is physically separated. A layered security approach enforces access to crypto modules, memory ranges, I/O pins, and other resources, and assures critical keys are available through hardware only with no access by software. The Root of Trust RT-1660 supports all commonly deployed host SoC processor architectures, including ARM, RISC-V, x86 and others.
Deep Anti-Tamper Experience
As the inventor and pioneer of DPA and an acknowledged leader in device security, Rambus is uniquely qualified to provide anti-tamper solutions for the most stringent requirements. Rambus technologies protect more than 9 billion chips per year, and as a US-based, independent company, Rambus has the experience and pedigree to be the solution provider of choice. Rambus has for more than 20 years supplied solutions for government and defense applications, including anti-tamper cores, software libraries, and testing workstations.

Introduction to Side-Channel Attacks
Side-channel attacks, including simple power analysis and differential power analysis, conducted against electronic gear are relatively simple and inexpensive to execute. An attacker does not need to know specific implementation details of the cryptographic device to perform these attacks and extract keys. As all physical electronic systems routinely leak information, effective side-channel countermeasures should be implemented at the design stage to ensure protection of sensitive keys and data.
Solution Offerings
- Custom-designed 32-bit secure RISC-V processor
- Multi-layered security model protects all core components against a wide range of attacks
- Security model includes hierarchical privilege model, secure key management policy, hardware-enforced isolation/access control/protection, error management policy
- State-of-the-art DPA resistance, FIA protection and anti-tamper techniques
- Standard hardware cryptographic accelerators, including AES (all modes), HMAC, SHA-2/-3 (all modes), RSA up to 8192 bits, ECC up to 521 bits, a NIST SP 800-90a/b/c compliant Random Bit Generator, AXI Interface and Fast DMA capability
- In addition to crypto modules a wide range of security modules such as canary logic for protection against glitching and overclocking, secure key derivation and key transport, life cycle management, secure test and debug, feature management are implemented
- Available in a dedicated FPGA configuration for synthesis in programmable logic, not relying on on-chip OTP
Complete Documentation
- Hardware integration guide
- Hardware and software reference manuals
- Programming guides
Tools and Scripts
- Verilog for synthesis and simulation
- All scripts and support files needed for standard EDA tool flows
Integration Deliverables
- Complete verification test bench and comprehensive set of test vectors
- Boot loader and firmware, including secure RTOS and security monitor
- HLOS APIs for accessing capabilities
- Complete development environment, including compiler, assembler, debugger, simulator, reference code