Root of Trust for FPGAs
Home > Security IP > Root of Trust Solutions > Root of Trust for FPGAs
FPGAs (Field Programmable Gate Arrays) are widely used in industries such as Defense, Telecommunications, Automotive and AI/ML (Artificial Intelligence/Machine Learning) because of their reconfigurability and flexibility. Whether functioning as the essential building blocks of avionics and spacecraft systems, controlling ADAS (Advanced Driver Assisted Systems) systems, or assisting inference workloads in AI/ML systems, FPGAs enable flexibility and faster development cycles.
Security is a widely recognized priority in all these applications. Rambus offers a solution that is tailored to the specificities of FPGAs with the Root of Trust for FPGAs (RT-630-FPGA). The Root of Trust is a siloed hardware security block, offering secure execution of user applications, tamper detection and protection, secure storage and handling of keys and security assets, resistance to side-channel attacks and many other security features. The Root of Trust features a 32-bit RISC-V secure processor and a number of high-capability cryptographic accelerators like AES-AE-16, HMAC 512, RSA 8K, ECC 521, RBG, Fast DMA, Whirlpool and a NIST SP800 compliant Random Bit Generator. Access to cryptographic modules, keys, memory ranges, I/O, and other resources occurs in the programmable logic. The Root of Trust is pre-integrated with industry-leading FPGA products such as the Xilinx Ultrascale family.
Security in the ARM Ecosystem
Building security in an SoC aiming to meet the goals set by the ARM Platform Security Architecture (PSA) is a complex matter. This is compounded by the complexity of modern-day SoCs comprising multiple processors, security domains and security levels. The Rambus root of trust provides a solid foundation for the SoC security architecture ticking ‘all the boxes’ for reaching the security goals, while offering extensive support for effective integration into a complex TrustZone-based SoC infrastructure.How the Root of Trust Works
The Rambus Root of Trust for FPGAs is optimized to run in an FPGA environment and leverages FPGA security features to ensure its confidentiality and integrity. The Rambus Root of Trust can run in parallel with additional domain specific logic in the same FPGA. The IP is pre-integrated with FPGAs from Xilinx and includes an FPGA Adaptation block. A user specifies its target, and Rambus delivers a synthesized bitstream that is ready to run on the platform designated. Rambus can also deliver RTL if the user desires to integrate the Rambus Root of Trust with its own domain-specific logic and generate a bitstream that includes both.
The Root of Trust for FPGAs requires the enablement of bitstream encryption and authentication on the target FPGA to ensure confidentiality and integrity. Encryption relies on AES-128 or AES-256, and symmetric authentication on AES-GCM or HMAC-SHA. Asymmetric authentication, when available, relies on RSA or ECC.
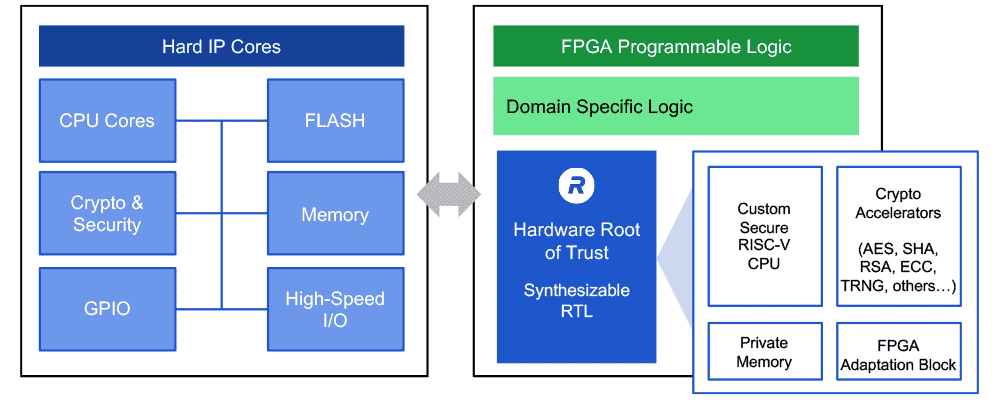
The Rambus Root of Trust for FPGAs uses flash memory or non-volatile memory embedded in the FPGA device (when available) to store keys and sensitive data required for its operation. The memory is encrypted using keys securely stored in the FPGA device. The FPGA adaptation block of the Root of Trust IP integrates the specific security components of the FPGA with it. It also enforces rollback protection to ensure that the content of the flash or embedded non-volatile memory cannot be read by an adversary and restored later to force the Root of Trust to a previous state.
Once running in the programmable logic, the Rambus Root of Trust for FPGAs provides access to a vast list of cryptographic algorithms, security services and secure applications.
Full Disk Encryption of Solid State Drives and Root of Trust
File encryption, file system encryption and full disk encryption (FDE) are methods offered by the industry to allow users to protect their data stored on non-volatile storage devices, such as Solid State Disks (SSD). The main feature of FDE is to protect stored system and user date from unauthorized reading, writing, alteration, moving or rolling back. However, extended security features are key to securing FDE implementation.