Differential power analysis is a powerful tool attackers used to extract secret keys and compromise the security of tamper resistant devices. DPA is a side-channel attack that is extremely effective low cost and widely known. These attacks use variations in the electrical power consumption of a targeted device and then breech security in devices by using statistical methods by deriving secret keys from crypto-algorithm. DPA attacks are dangerous because they circumvent the normal hardware and software security defenses that have been put in place, allowing fraudulent transactions, data theft, device modifications and other costly, unauthorized activities. Because such attacks are noninvasive, an intruder can compromise an embedded system without leaving a trace.
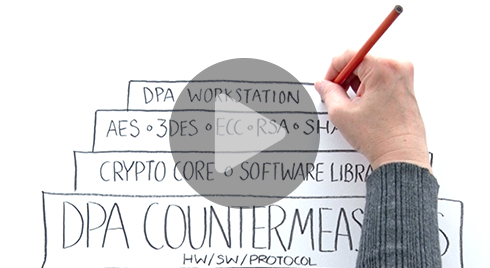
To learn how Rambus Security is guarding DPA attacks, click here.