Home > Security IP > CryptoMedia Content Security Platform > CryptoMedia Player Agent
Security
CryptoMedia Player Agent
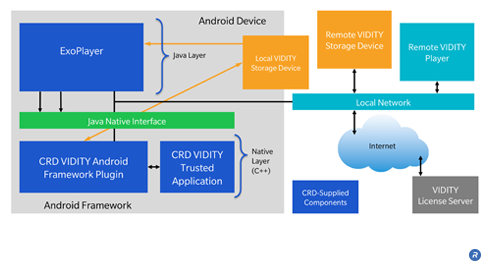
Designed as a secure software foundation for premium digital content players, the CryptoMedia Player Agent delivers an easy-to-integrate solution for the secure acquisition and playback of 4K Ultra High Definition (UHD) High Dynamic Range (HDR ) content
How CryptoMedia Player Agent works
Part of the complete CryptoMedia platform that includes the Key Derivation Core and Key Issuance Center, the CryptoMedia Player Agent as an easy-to-integrate, secure software solution for embedded media players in consumer electronics, including Connected TVs, STBs, BluRay players, and mobile devices. The Player Agent meets all relevant requirements for secure implementation in Android or Linux operating systems. It combines both secure and insecure elements, performing non-security-critical functions, and security-critical functions in a Trusted Execution Environment (TEE) or secure processor.
The Player Agent is designed to enable highest digital content ownership experience and is available standalone or integrated with the CryptoMedia Key Derivation Core.
Solution Offerings
• Pre-compiled, device-specific Agent libraries
• Reference application source code
• Full documentation
• Optional porting and integration support