The rapid growth of connected devices and the sensitive data they generate poses a significant challenge for manufacturers seeking to comprehensively protect their devices from attack. Indeed, consumers expect their IoT devices and data to be adequately secured against a wide range of vulnerabilities and exploits. Put simply, high levels of security must now be implemented as a primary design parameter, rather than a tertiary afterthought.
Historically, solutions that included robust encryption/decryption algorithms with cryptographic keys were considered secure. This is because brute force attacks have ultimately become computationally infeasible due to the increased key length of the cryptographic algorithm.
Nevertheless, there is a category of attacks that simply ignore the mathematic properties of a cryptographic system – instead focusing on its physical implementation in hardware. More specifically, cryptographic systems routinely leak information about the internal process of computing. In practical terms, this means attackers can exploit various techniques to extract the key and other secret information from the device.
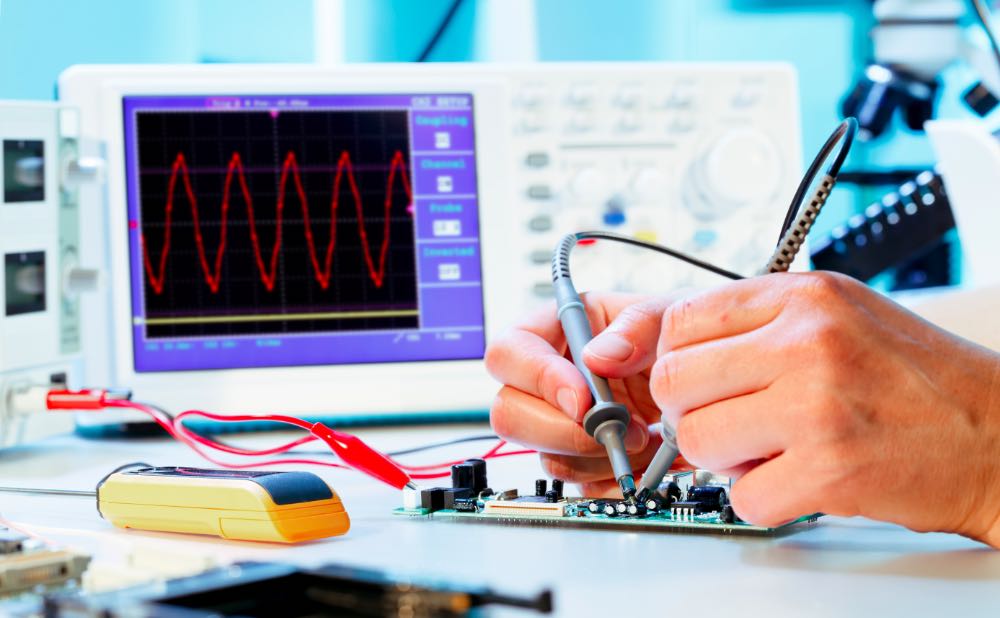
This vector is known as side-channel attacks, which are commonly referred to as SCA. Essentially, side-channel attacks monitor power consumption and electro-magnetic emissions while a device is performing cryptographic operations. Side-channel attacks conducted against electronic devices and systems are relatively simple and inexpensive to execute. This means attackers can exploit various side-channel techniques to gather data and extract secret cryptographic keys.
According to YongBin Zhou and DengGuo Feng, one of the earliest instances of side-channel attacks occurred in 1965 when the British MI5 agency attempted to crack a cipher used by the Egyptian Embassy in London. After its efforts were thwarted by the limitations of mid-20th century computational power, a scientist by the name of P. Wright suggested placing a microphone near the rotor-cipher machine used by the Egyptians to monitor the click-sounds the device produced. By carefully listening to the clicks of the rotors as cipher clerks reset them each morning, MI5 agents managed to successfully deduce the core position of two or three of the machine’s rotors. This additional information significantly reduced the computation effort needed to break the cipher, enabling MI5 to effectively spy on the embassy’s communication for years.
Modern side-channel techniques were pioneered by Paul Kocher in the late 1990’s when the scientist observed that the mathematics of a cryptosystem could be effectively subverted.
“Integrated circuits are built out of individual transistors, which act as voltage-controlled switches. Current flows across the transistor substrate when charge is applied to (or removed from) the gate. This current then delivers charge to the gates of other transistors, interconnect wires and other circuit loads. The motion of electric charge consumes power and produces electromagnetic radiation, both of which are externally detectable,” Kocher wrote in 1998.
“Therefore, individual transistors produce externally observable electrical behavior. Because microprocessor logic units exhibit regular transistor switching patterns, it is possible to easily identify macro-characteristics (such as microprocessor activity) by the simple monitoring of power consumption. DPA type attacks perform more sophisticated interpretations of this data.”
Keep on reading: Side-channel attacks explained »
