Did you know that millions of implanted medical devices (IMDs) do not typically receive software upgrades to address security vulnerabilities? Such devices – which are often connected via the internet or wireless technologies – include cardiac pacemakers, insulin pumps and brain neurostimulators. Consequently, IMDs pose very clear risks along with their obvious benefits.
“Hackers who gain access to confidential patient information could use malware as ‘ransomware,”’ writes Jill Goetz of the Arizona Engineer. “Worse, they could put a patient with an implanted cardiac pacemaker – there are more than 225,000 such people in the United States alone – into cardiac arrest.”

According to Roman Lysecky, an associate professor in the University of Arizona Department of Electrical and Computer Engineering, such an event hasn’t happened yet. However, says Lysecky, security researchers have proved it is possible.
As Goetz reports, Lysecky is pioneering technology that would enable IMDs to detect malware and continue functioning even if security is breached.
“We believe manufacturers should build implantable medical devices like pacemakers with malware detection strategies from the get-go and provide patches as future problems develop,” Lysecky told the publication.
In addition to developing a malware detection system to protect IMDs, Lysecky is working on another project (with an Army Research Office grant) to help protect medical implants against side-channel attacks. More specifically, he and co-principal investigator Janet Meiling Roveda, UA professor of electrical and computer engineering, are developing mathematical models to analyze changes in timing, power consumption and electromagnetic radiation.
“Side-channel attacks like these are a critical threat to the security of embedded systems,” Lysecky said. “By analyzing data transmission timing, power consumption and electromagnetic radiation from a life-critical device such as a pacemaker, a hacker can extract data like cryptographic keys that are essential for shielding communications from unauthorized users.”
As we’ve previously discussed on Rambus Press, all physical electronic systems routinely leak information about their internal process of computing. In practical terms, this means attackers can exploit various side-channel techniques to gather data and extract secret cryptographic keys. Regardless of specific instruction set architecture (ISA), most industry security solutions on the market today can be soundly defeated by side-channel attacks. Even a simple radio is capable of gathering side-channel information by eavesdropping on frequencies emitted by electronic devices. In some cases, secret keys can be recovered from a single transaction clandestinely performed by a device several feet away.
One notable side-channel attack technique is Differential Power Analysis (DPA), a form of side-channel attack that monitors variations in the electrical power consumption or electro-magnetic emissions of a target device. The basic method involves partitioning a set of traces into subsets, then subsequently computing the difference of the averages of these subsets. Given enough traces, extremely minute correlations can be isolated—no matter how much noise is present in the measurements.
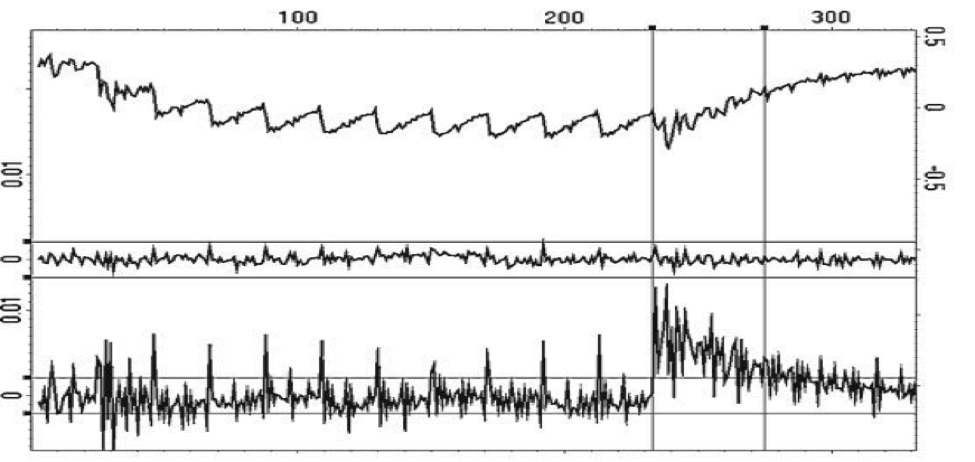
Image Credit: Rambus Security Division (via “Introduction to Differential Power Analysis”)
A typical DPA attack comprises 6 primary stages: communicating with a target device; recording power traces while the target device performs cryptographic operations; signal processing to remove errors and reduce noise; prediction and selection function generation to prepare and define for analysis; as well as computing the averages of input trace subsets and evaluating DPA test results to determine the most probable key guesses. Additional DPA variants include reverse engineering unknown S-boxes and algorithms, correlation power analysis (CPA), probability distribution analysis, high-order DPA and template attacks.
Specific DPA countermeasure techniques include decreasing the signal-to-noise ratio of the power side channel by reducing leakage (signal) or increasing noise, for example, by making the amount of power consumed less contingent upon data values and/or operation (balancing); introducing amplitude and temporal noise; incorporating randomness with blinding and masking by randomly altering the representation of secret parameters and implementing protocol-level countermeasures by continually refreshing and updating cryptographic protocols used by a device.
Interested in learning more about protecting electronic systems against side-channel attacks? You can check out our DPA countermeasures product page here.

Leave a Reply