PKA-IP-150 RSA/ECC Public Key Accelerators
Home > Security IP > Crypto Accelerator Cores > PKA-IP-150
The PKA-IP-150 is a family of Public Key Accelerators (PKA) IP cores designed for full scalability and an optimal “performance over gate count” deployment. Silicon-proven, the PKA-IP-150 address the unique high-speed, high-security requirements of semiconductor OEMs and provides a reliable and cost-effective IP solution that is easy to integrate into SoC designs. The PKA-IP-150 can be deployed in any semiconductor design that requires high performance key exchange or key generation with low power consumption, and can be provided with or without protection against side channel attacks.
The PKA-IP-150 public key accelerator combines the PKA-IP-28 and TRNG-IP-76 with an AMBA interface such as AXI or AHB.
Up to 4160-bit modulus size for RSA & 768-bit modulus for prime field ECC operations
Public key signature generation, verification and key negotiation with little involvement of host
NIST CAVP compliant for FIPS 140-3
How the PKA-IP-150 works
The PKA-IP-150 accelerates the following basic operations in hardware:
- Large vector addition, subtraction and combined addition/subtraction
- Large vector bit shift right or left
- Large vector multiplication, modulo and division (the latter generates both remainder and quotient)
- Large vector compare and copy
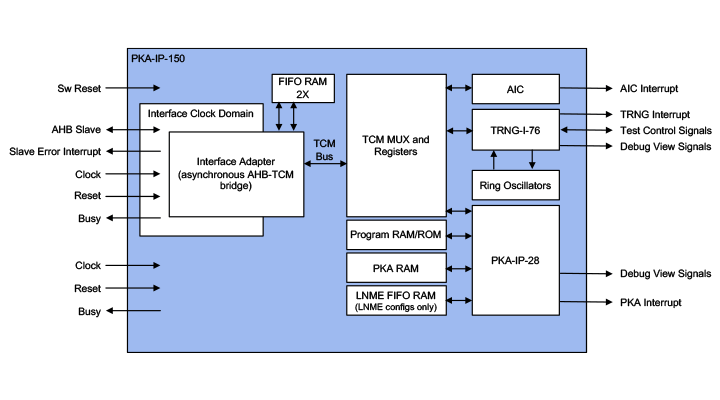
The included PKA-IP-28 core also accelerates the following complex operations, under control of an embedded sequencer microcontroller, using locally stored firmware:
- Large vector unsigned value modular exponentiation
- Large vector unsigned value modular exponentiation using the ‘Chinese Remainders Theorem’ (‘CRT’) method with pre-calculated Q inverse vector
- Modular inversion: given A and M, calculate B such that ((AB) MOD M) = 1
- Prime field ECC point addition/doubling on elliptic curve y2=x3+ax+b (mod p) with ‘p’ a prime number and ‘a’ and ‘b’ input values to the operation, adding identical points automatically performs point doubling – operation can be performed with affine and projective points
- Prime field ECC point multiplication on elliptic curve y2=x3+ax+b (mod p) with ‘p’ a prime number and ‘a’ and ‘b’ input values to the operation – a version of the ‘Montgomery ladder’ algorithm, point randomization and point-on-curve checking are used to provide side channel attack protection The Sequencer firmware hides the fact that the modular exponentiations and ECC point multiplication are done using numbers in the Montgomery domain. For improved performance of modular exponentiation operations, the Public Key Accelerator employs exponent recoding techniques that use a table with pre-calculated odd powers (filling this table is performed by the sequencer firmware). The smallest configurations can optionally use the ‘Montgomery Ladder’ algorithm for modular exponentiation (lower performance but fixed timing).

Introduction to Side-Channel Attacks
Side-channel attacks conducted against electronic gear are relatively simple and inexpensive to execute. Such attacks include simple power analysis (SPA) and Differential Power Analysis (DPA). As all physical electronic systems routinely leak information, effective side-channel countermeasures should be implemented at the design stage to ensure protection of sensitive keys and data.
PKA-IP-150 Applications
PKA-IP-150 public key accelerators are suitable for a wide range of applications:
- IoT, mobile, or other small gate count applications for secure boot, software public key signature checking and ‘occasional’ public key operations as used for IPsec and MACsec channel setup and firmware download signatures
- Secure router boxes, secure network interfaces and SSL servers, where the PKA-IP-150 is used in medium to high performance (Elliptic Curve) Diffie-Hellman key negotiation engines
- Hardware security modules, used in medium to high performance secure public key signature generator/checker engines
The PKA-IP-150 is available in nine different performance configurations, ranging from 40K to 555K gates, each providing the full set of TRNG and PKA operations. The offer up to 4160-bit modulus size for modular exponentiations and 768-bit modulus for prime field ECC operations. The PKA-IP-150 is a security conscious design and can be provided with or without protection against side channel attacks.