Home > Security IP > DPA Countermeasures
DPA and FIA Countermeasure Solutions
After discovering Simple Power Analysis (SPA) and Differential Power Analysis (DPA), Rambus developed fundamental DPA countermeasure solutions and techniques for protecting devices against DPA and related side-channel attacks, along with supporting tools, programs, and services. In addition, cores are available that add Fault Injection Attack (FIA) protection while maintaining DPA resistance levels.
| Solutions | Product Brief | Applications |
|---|---|---|
| DPA Resistant Cores | Commercial, Government | |
| Licensed Countermeasures | Commercial, Government |
Protecting Electronic Systems from Side-Channel Attacks

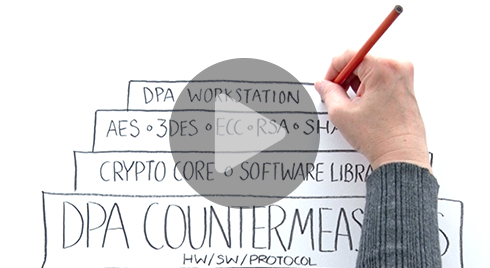
DPA Countermeasures
Many electronic devices that use cryptography are susceptible to side-channel attacks, including SPA and DPA. A side-channel is an unintentional channel providing information about the internal activity of the chip, for example power consumption or EM emissions.
These low-cost, non-invasive methods enable attackers to stealthily extract secret cryptographic keys used during normal device operations. Once the keys have been extracted, attackers can easily gain unauthorized access to a device, decrypt or forge messages, steal identities, clone devices, create unauthorized signatures and perform additional unauthorized transactions.
Many electronic devices that use cryptography are susceptible to side-channel attacks, including SPA and DPA. A side-channel is an unintentional channel providing information about the internal activity of the chip, for example power consumption or EM emissions. These low-cost, non-invasive methods enable attackers to stealthily extract secret cryptographic keys used during normal device operations. Once the keys have been extracted, attackers can easily gain unauthorized access to a device, decrypt or forge messages, steal identities, clone devices, create unauthorized signatures and perform additional unauthorized transactions.
Billions of devices deployed across numerous industries already meet stringent standards for side-channel resistance. Many use our IP cryptographic cores and software libraries to protect against DPA and related side-channel attacks.
As part of our ecosystem enablement, we offer our DPA Workstation™ Platform to customers and partners as a powerful and flexible tool for evaluating the level of DPA resistance within a device or system. It includes customized test fixtures and a proprietary DPA software suite with source code.
Additionally, we have established a comprehensive third-party validation program to certify the DPA resistance of cryptographic modules for SoCs, systems manufacturers and testing labs.
Introduction to Side-Channel Attacks

Side-channel attacks conducted against electronic gear are relatively simple and inexpensive to execute. Such attacks include simple power analysis (SPA) and Differential Power Analysis (DPA). As all physical electronic systems routinely leak information, effective side-channel countermeasures should be implemented at the design stage to ensure protection of sensitive keys and data.



