Earlier this month, Christopher Gori, a senior director of product management in Rambus’ security division, wrote an article for Semiconductor Engineering about the evolution of side-channel attacks.
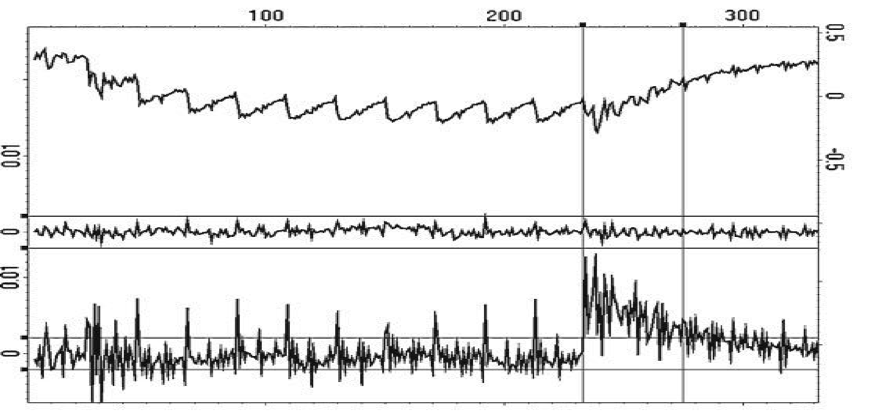
As Gori explains, a side-channel attack can perhaps best be defined as any attack based on information gained from the physical implementation of a cryptosystem, rather than brute force or theoretical weaknesses in the algorithms. To be sure, all physical electronic systems routinely leak information about their internal process of computing via power consumption or electromagnetic emanations. This means attackers can exploit various side-channel techniques to gather data and extract secret cryptographic keys.
“Whether implemented in hardware or software, and regardless of specific instruction set architecture (ISA), most cryptographic security solutions on the market today can be soundly defeated by side-channel attacks,” he writes. “In some cases, secret keys can be recovered from a single transaction clandestinely performed by a device several feet away.”
According to Gori, single-chip devices such as smart cards initially received much of the side-channel attention in the attacker community due to the ubiquity of smart cards in low-end commerce applications and the relatively low cost of such an attack vector. With the side-channel landscape steadily evolving over the years, attackers are now capable of compromising a wide variety of vulnerable targets such as aerospace and defense systems, vehicles, set-top boxes and even implanted medical devices.
As more devices are connected to the Internet of Things (IoT), says Gori, proactive suppliers have begun to place more of an emphasis on security by offering integrated countermeasures to their customers.
“[This is because] devices without countermeasures are frequently vulnerable to Differential Power Analysis (DPA), a category of noninvasive side-channel attack. Effective DPA resistance cannot be achieved by chance, or even by the default complexity or high clock frequency of a target device,” he explains. “Therefore, measurable and quantifiable security standards, such as those offered by Test Vector Leakage Assessment (TVLA) methodology, are essential to shielding devices and systems from side-channel attacks, as untested and unverified countermeasures are typically ineffective.”
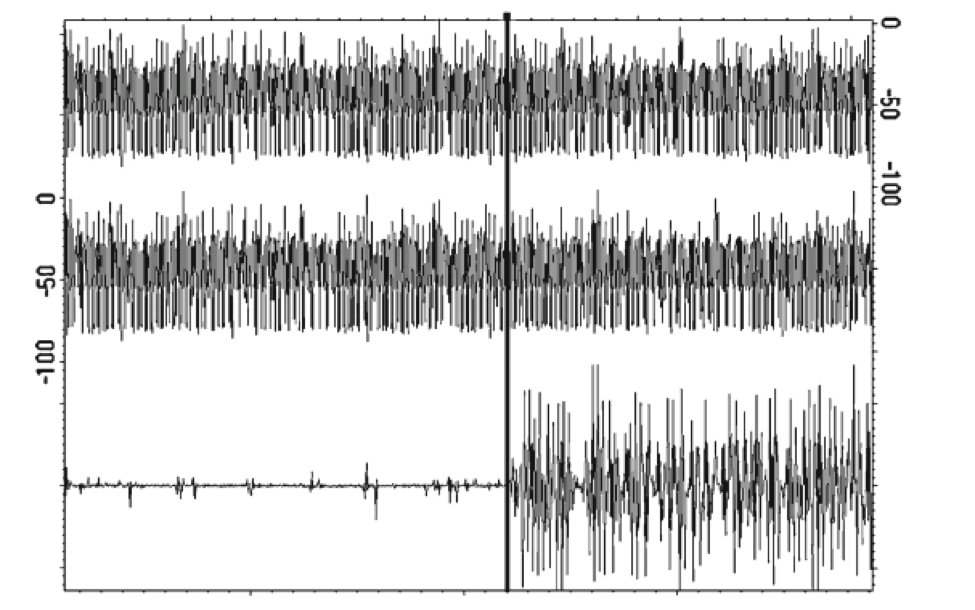
Specific DPA countermeasure techniques, says Gori, include decreasing the signal-to-noise ratio of the power side channel by reducing leakage (signal) or increasing noise, for example, by making the amount of power consumed less contingent upon data values and/or operation (balancing); introducing amplitude and temporal noise; incorporating randomness with blinding and masking by randomly altering the representation of secret parameters and implementing protocol-level countermeasures by continually refreshing and updating cryptographic keys used by a device.
“Device vendors can either implement countermeasures themselves or choose from several commercial software and hardware offerings that provide side-channel resistant for commonly used cryptographic offerings,” he adds. “For device makers implementing DPA countermeasures, it is recommended that the system and device prototypes be evaluated for resistance to side-channel attacks – such as SPA, CPA, DPA, HO-DPA and their electromagnetic equivalents – before a product is brought to market.”
Interested in learning more? You can check out our DPA countermeasures page here.
