Small devices, comprehensive protection
Cryptography experts at the National Institute of Standards and Technology (NIST) have kicked off an initiative to protect IoT devices that require a new class of cryptographic defenses against cyber-attacks. More specifically, the creation of such defenses is the goal of NIST’s lightweight cryptography initiative – which aims to develop cryptographic algorithmic standards that can function within the limited confines of a simple electronic device.

“Many of the sensors, actuators and other micromachines that will function as eyes, ears and hands in IoT networks will work on scant electrical power and use circuitry far more limited than the chips found in even the simplest cell phone,” NIST stated in a recent press release. “Similar small electronics exist in the keyless entry fobs to newer-model cars and the Radio Frequency Identification (RFID) tags used to locate boxes in vast warehouses.”
Lightweight encryption standards
As part of the initiative, NIST is seeking assistance in developing requirements and guidelines for such solutions. The “Draft Submission Requirements and Evaluation Criteria for the Lightweight Cryptography Standardization Process” is the first draft of this request – and can be downloaded here from the NIST website.
The ultimate goal, says NIST computer scientist Kerry McKay, is to develop lightweight encryption standards that benefit the entire market.
“The IoT is exploding, but there are tons of devices that have nothing for security,” McKay explained. “There’s such a diversity of devices and use cases that it’s hard to nail them all down. There are certain classes of attacks to consider, lots of variations. Our thinking had to be broad for that reason.”
According to McKay, the NIST team spent four years consulting with various industry groups, ranging from smart power grid experts to auto manufacturers. Their advice prompted the team to stipulate that submitted algorithms must have been published previously and been analyzed (though not necessarily adopted) by a third party.
“We feel it’s a fair request because people have been working on crypto for constrained environments for several years now,” McKay added. “We want to see things that the world has looked at already.”
Authenticated encryption with AEAD
These solutions, says McKay, typically utilize symmetric cryptography – with both the sender and recipient having an advance copy of a digital key that can encrypt and decrypt messages. However, the NIST team specifies that these algorithms should also provide authenticated encryption with associated data (AEAD), which allows a recipient to check the integrity of both the encrypted and unencrypted information in a message.

In addition, NIST researchers stipulate that if a hash function is used to create a digital fingerprint of the data, the function should share resources with the AEAD to reduce the cost of implementation.
Side-channel attack countermeasures
Moreover, the “Draft Submission Requirements and Evaluation Criteria for the Lightweight Cryptography Standardization Process” specifies that the implementations of the AEAD algorithms and the optional hash function algorithms should lend themselves to countermeasures against various side-channel attacks (SCA), including timing attacks, simple and differential power analysis (SPA/DPA), as well as simple and differential electromagnetic analysis (SEMA/DEMA).
As we’ve previously discussed on Rambus Press, all physical electronic systems routinely leak information about the internal process of computing via fluctuating levels of power consumption and electro-magnetic emissions.
Much like traditional safecracking, electronic side-channel attacks eschew a brute force approach to extracting keys and other secret information from a device or system. As such, SCA conducted against electronic devices and systems are non-intrusive, relatively simple and inexpensive to execute.
An effective layer of side-channel countermeasures should therefore be implemented via hardware (DPA resistant cores), software (DPA resistant software libraries) or both. Countermeasures – including leakage reduction, noise introduction, obfuscation and the incorporation of randomness – are critical to ensuring the protection of sensitive keys and data. It should be noted that stand-alone noise introduction is incapable of sufficiently masking side-channel emissions. Indeed, DPA conducted against a device can effectively bypass stand-alone noise countermeasures, ultimately allowing the signal to be isolated.
TVLA and Rambus DPAWS
After layered countermeasures have been implemented, systems should be carefully evaluated with a Test Vector Leakage Assessment (TVLA) platform such as the Rambus DPA Workstation (DPAWS) to confirm the cessation of sensitive side-channel leakage.
More specifically, DPAWS measures a range of side-channel attacks across a wide spectrum of devices and platforms including smart phones, tablets, POS terminals, CPUs, TVs, set-top boxes, FPGAs, smart cards and NFC tech. DPAWS provides users with a highly-intuitive UI paired with enhanced data visualization that creates an integrated, project-centric analytic environment specifically designed to optimize the efficiency of side-channel analysis.
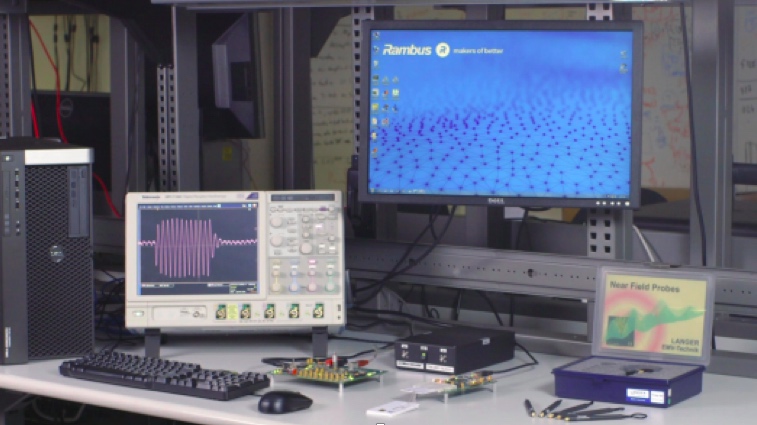
Both flexible and scalable, DPAWS supports multiple side-channel sensors, device protocols and form factors, with out-of-the-box support for SASEBO and additional third-party hardware. DPAWS also easily integrates with a wide range of industry tools including Matlab, Python and other scripting languages. Moreover, the Rambus DPA Workstation supports full cipher coverage (AES, RSA, ECC, DES and SHA), large dataset handling, as well as high-speed collection and analysis of billions of traces. Source code is also available to facilitate increased flexibility.
Interested in learning more about protecting electronic systems from side-channel attacks? You can download our eBook on the subject below.


Leave a Reply