
Rambus AES-32 Cryptographic Accelerator IP Core Is Common Criteria Certified
Following on from the recent news that Rambus HQ has been Common Criteria (CC) certified,

Following on from the recent news that Rambus HQ has been Common Criteria (CC) certified,
What products achieved PCIe 5.0 compliance? At the most recent PCI-SIG® Compliance Workshop held in

The fifth annual AI Hardware Summit was back this month, and for the first time

As a leading provider of security IP, Rambus invests time and effort in certification, and

While server virtualization is being widely deployed in an effort to reduce costs and optimize

The CXL™ Consortium (of which Rambus is a member) has now released the 3.0 specification
1. Introduction As silicon manufacturing process nodes keep shrinking and transistors get smaller, System-on-Chip (SoC)
The first wave of DDR5-based servers sport RDIMMs running at 4800 megatransfers per second (MT/s).

Rambus Fellow, Steven Woo, returns to the Rambus Design Summit stage tomorrow, and we are

We’re so excited that Ann Keffer, Product Marketing Manager at Siemens EDA, will be joining
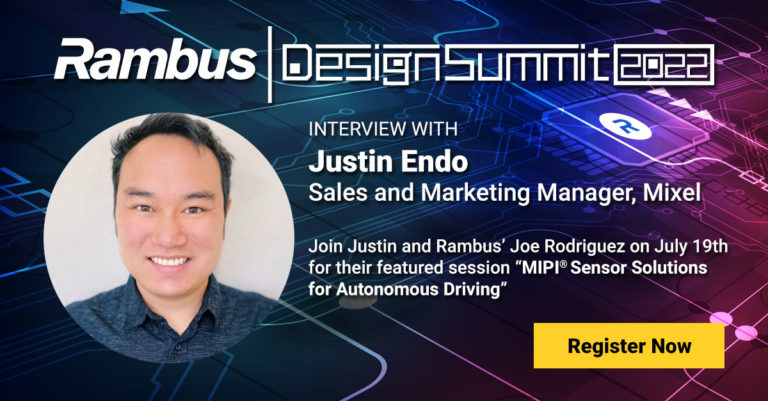
Our partner from Mixel, Justin Endo, is joining us at Rambus Design Summit and we
Formerly known as the Society of Automotive Engineers, SAE International is a global professional association

Semiconductor scaling has been a boon without equal to the world of computing. But with

The Rambus CSI-2 Transmitter (Tx) Controller has received ISO-26262 functional safety certification at the Automotive

Over-the-air (OTA) programming refers to the ability to download applications, services, and configurations over a

Rebuilding Together Peninsula (RTP) is a nonprofit organization that provides free repairs to low-income homeowners

A self-driving car is a computer-controlled vehicle that drives itself. Also referred to as an
The Compute Express Link™ (CXL) Consortium has invited Vincent Haché, Director of Systems Architecture at

At GOMACTech 2022, Scott Best, director of anti-tamper security technology at Rambus will present “Advanced

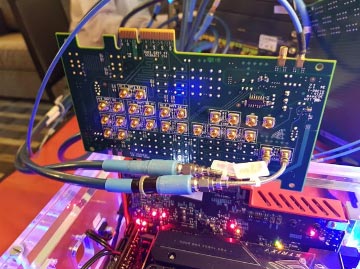
With the ever-increasing complexity of the PCI Express® Gen5/6 and CXL™ protocols, integrating next-generation IP

The functional safety of automotive electronics is governed by ISO 26262 with a hierarchy of
